What is Crypto Forensics?
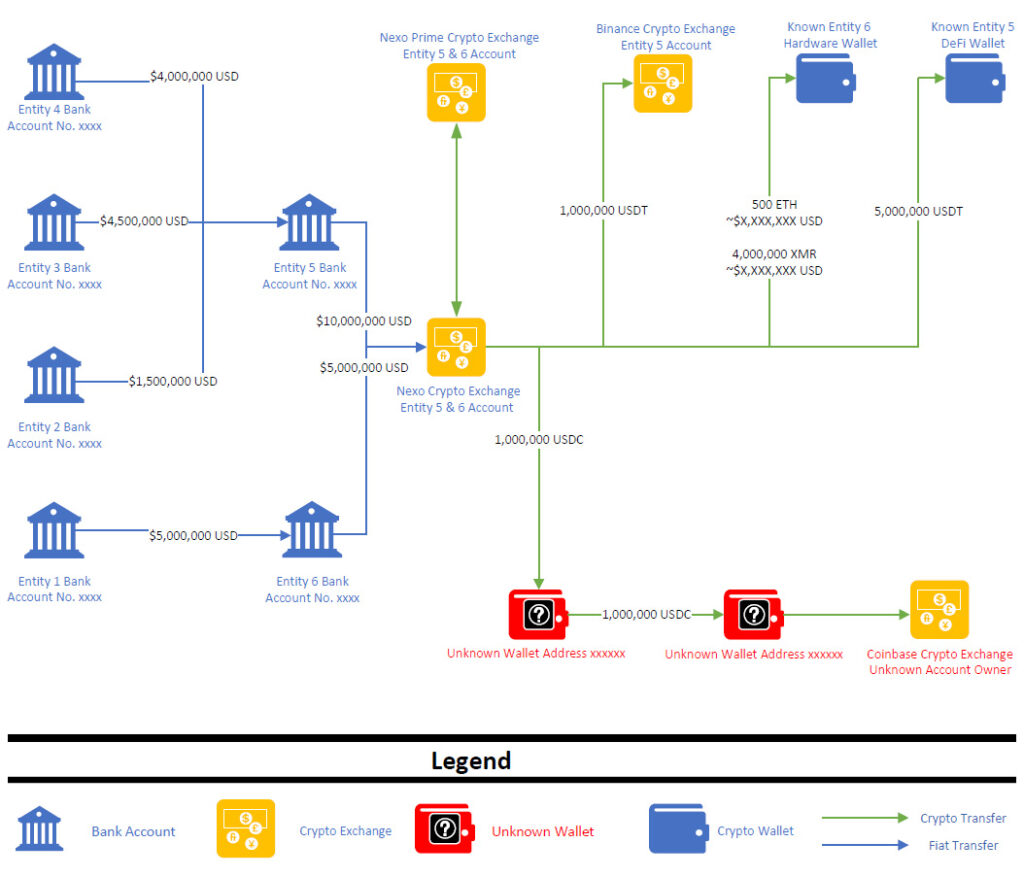
Crypto forensics is the application of digital forensic science on blockchains to trace and recover cryptocurrency assets and evidence. Blockchains serve as a secure ledger of cryptocurrency transactions and support monitoring. Many people believe crypto is anonymous, but in reality it can be recovered and traced. Crypto forensics traces are artifacts or fragments recovered from forensically sound copies, or images, of computers or mobile devices on which the user executed cryptocurrency transactions or stored addresses in wallets. What kind of evidence from crypto investigations can forensic accountants, attorneys, and investigators expect to be forensically collected for review?
Crypto evidence is full of metadata. Metadata is data about the data. Metadata recovered from crypto wallet forensics might contain information about important digital cryptocurrency assets including addresses and their formats, totals sent and received, account balances, and date and time stamps for when crypto events or transactions might have taken place. In a crypto exchange transaction the metadata might include the transaction ID, the address of a cryptocurrency transfer from a wallet to an exchange, or between exchanges, and possibly, fees.
Cryptocurrency Forensics and Investigations
As worldwide demand for cryptocurrency grows, financial institutions and businesses that embrace it will eventually have needs to understand, trace, and determine where, when, how, and by whom cryptocurrency was fraudulently exploited, abused, or outright stolen. With their unique skillsets experienced forensic accountants and digital forensic experts are uniquely qualified to recover crypto assets and track coins thorough investigations that provide clarity for clients and their trial lawyers.
As part of digital forensic investigations, digital or electronic devices like computers, smartphones, hardware wallets, or other devices must be forensically imaged to recover crypto evidence as part of an investigation.
Digital forensic experts are ready to detect, extract, and analyze cryptocurrency artifacts in mobile device and computer forensic investigations using open source and commercial tools. They find hidden cryptocurrency wallet files in memory and on disk, and know how to recover an encrypted crypto wallet. Crypto forensics experts are skilled in recovering cryptocurrency from hardware wallets, often called cold storage. They know how to extract private and public keys and how to legally collect a custodian’s crypto wallet.
Common Crypto Investigations and Goals
Common investigations for which forensic accountants and digital forensic experts are engaged in 2026 include:
- Probate of Trusts and Estates (Recover Crypto Assets)
- Marital Dissolution (Hidden Crypto Assets)
- Investors (Ponzi Schemes)
- Fraudulent Crypto Conveyances
- Embezzlement or Theft of Crypto Assets
- Bankruptcy
- Insurance Claims
- Tax Fraud
- Litigation Support
Crypto forensic investigation goals may include:
- Tie crypto asset transactions to identified person(s)
- Identify current location of crypto assets (crypto exchange, hardware/software/web wallet, paper)
- Reveal crypto facts and material evidence to stakeholders, litigants, or insurance companies
- Identify and quantify crypto losses and damages
- Crypto forensics recovery and repatriation of funds
Crypto Wallet Forensics Recovers Assets

Crypto wallets supported by Carney Forensics’ digital forensics tools include those depicted above:
- Coinbase Wallet
- Bitcoin Core Client
- Coinomi
- Bread Wallet
- Beam Wallet
- Exodus
- Crypto.com Wallet
- Visa Qiwi Wallet
- Jaxx Blockchain Wallet
- Metamask
- BitPay
- Trust Wallet
- MyEtherWallet (Mew)
Crypto investigators must be alert to detect and recover both known and unknown crypto wallets. They use one or more tools as part of a forensic tool kit to effectively scan and parse cryptocurrency traces and transactions conducted by a custodian on his or her computer or smartphone.
Crypto forensics experts must be alert to recognize and isolate “Pocket litter” or other lists of seemingly random words. They are typically twelve in number, but some wallets can support seed phrases up to 33 words. If used in the correct order, these words can recover a crypto wallet. “Recovery seeds” or “seed phrases” may be hidden within books, planners, or unrelated notes. Or, they can be in plain sight as clear lists, metal storage backups, or cold storage wallets.
Experts who practice Bitcoin forensics must evaluate pocket litter for Bitcoin ATM receipts. While many of these receipts will say “Bitcoin” or some “bit” derivative, some Bitcoin ATM receipts are less conspicuous than others. In more inconspicuous cases, phrases such as “ledger balance” tip the examiner off to crypto usage.
Crypto Exchange Forensics Recovers Transactions

Crypto exchange forensics is supported by Carney Forensics’ digital forensics tools, including those depicted above:
- Coinbase
- BRD
- Beam Exchange
- Exodus
Two-factor authentication (2FA) is a common practice to secure user accounts at cryptocurrency exchanges. Crypto forensics experts recover and analyze authenticator apps like Google, Microsoft, and Authy to reveal ties to specific crypto exchanges. See the one-time 2FA code for a Coinbase crypto exchange account below:
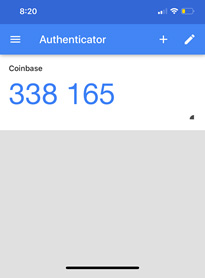
Google Authenticator codes like this indicate an association with a cryptocurrency exchange like Coinbase.
Recover Crypto Evidence from Computer or Mobile Device Artifacts
Crypto forensics experts recover bank accounts, both known and unknown, by examining browser cache, Google searches, parsed search queries, and third party mobile apps for banks. The same applies to financial services companies, credit unions, etc.
They also recover crypto emails and text messages from computer hard drive images or smartphone extractions which may contain receipts of transactions or transfers. Data from these devices may provide evidence such as cryptocurrency obtained, exchanges utilized, and which hardware wallets may have been used for storage and payment purposes.
Crypto forensics experts recover photographs and screenshots from forensic images or extractions of devices that may contain clues to crypto assets. A manual review of a custodian’s photographs on a computer or mobile device may reveal valuable information such as recovery seeds, specific transactions, or wallet and exchange services used. A crypto investigator taking advantage of an advanced digital forensic tool’s machine learning algorithms that recognize and categorize device screenshots automatically is a faster and more cost-effective approach for identifying and recovering crypto evidence.
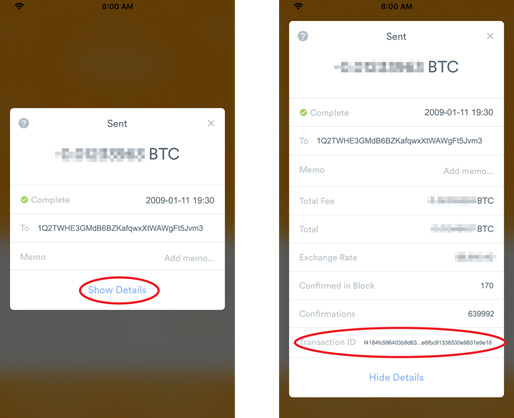
These redacted smartphone screenshots show a custodian’s Bitcoin transaction sent through the BRD app.


