Cell phone experts at Carney Forensics began recovering text messages and phone contact lists from old flip phones back in 2008. Over a decade and a half has passed, and hundreds of cell phones in our lab have given up their secrets. New powerful cellular phone forensics tools have delivered breakthrough capabilities for evidence recovery from smartphones using iPhone and Android forensics services. Cell phones have become the new DNA with the power to recover compelling, truthful evidence in proof of cases in courts across America.
What is Cell Phone Forensics?
Cell phone forensics is the process of recovering, analyzing, and producing digital evidence from modern smartphones like iPhones and Androids, but also legacy devices like BlackBerry and Windows Phones. It also applies to old feature phones, flip phones, and burners. Cellular forensics involves using specialized tools and forensically sound methods to perform phone imaging, including handset memory, network data from physical or electronic SIM cards, and external storage media on a microSD card.
Cellular phone forensics aims to recover and preserve relevant, even material, evidence from mobile devices. It does so in a forensic manner compliant with the rules of evidence such that it becomes admissible in a court of law and can assist juries and judges in criminal and civil litigation. The forensic cell phone data analyzed to develop probative findings may be live or deleted, including information fragments or trace evidence.
An essential difference between cell phone forensics and traditional computer forensics is the devices and their evidence are no longer stationary, isolated, and static. Cell phone evidence is dynamic and mobile because the devices reach out to the world’s cell towers, low earth orbit GPS navigation satellites, Wi-Fi networks, and the public Internet. They also connect with other devices through nearby Bluetooth and Near Field Communication signals. When powered on, they receive and process information from multiple external sources and use hundreds of mobile apps to prepare it for the cell phone user’s consumption.
Cell phone forensics is evolving at an accelerating pace and continues to change with advancements in cellular and communications technology. New cellular devices, operating systems, mobile apps, cybersecurity, and encryption features are introduced for the user’s safety and privacy. Cellphone forensics experts must adapt to these advancements and learn new tools and forensically sound methods to move forward quickly and keep up with the technology.
What Evidence Can Cell Phone Forensics Recover?
Our cell phone investigators recover, analyze, and produce evidence of many types, including these categories:
Four Types of Cell Phone Evidence Starting with Phone Contacts List
Cell phone evidence is digital evidence recovered forensically from smartphones and tablets. Think Apple’s iPhones and iPads, as well as Android smartphones and tablets from manufacturers like Samsung, Motorola, and LG. The phone contacts list is basic cell phone evidence. A decade ago, feature phones, sometimes called flip phones, contained a trivial amount of contact evidence. Those phone contacts lists contained a person’s name, a cell phone number, and usually nothing else.
Today’s smartphones provide rich information about the phone user’s contacts. These contacts can be complex, containing a person’s name but also aliases, credentials, phone numbers, email addresses, website addresses, social media accounts, street addresses, employment information, and so on. The phone contacts list becomes a directory of actors and players for use by the lawyer and his or her cell phone forensic expert during the pendency of the case.
Call Logs
Call log evidence is a record of phone call metadata, not a voice audio recording. It contains phone numbers to and from the smartphone, often with a user’s name matching the phone number taken from the phone contacts list. It also includes a date and time stamp and the duration of the phone call in minutes and seconds.
Voice Messages
When a phone user checks his or her voice messages, those messages are downloaded to the smartphone from the cell phone service provider. They are stored in the smartphone’s file system as live evidence, and when deleted by the phone user, they are often still recoverable. Sometimes, the smartphone transcribes voice message recordings accurately and produces a readable, textual record. When cases go to trial, our cell phone expert witnesses play admissable voice message audio, which is often persuasive in the courtroom, especially if deleted.
Device Locations
Device locations are important geolocation evidence. GPS data containing latitude and longitude coordinates sourced from navigation satellites and stored in the smartphone often include elevation and, occasionally, speed or velocity. This evidence is essential in motor vehicle and truck accidents to show vehicle paths. It is also useful in criminal justice cases to establish proof at the scene of a crime or an alibi.
Cell phone investigators find GPS device locations embedded in photographs, videos, and Wi-Fi networks. They can also be found in navigation apps like Google Maps or Apple Maps and social media apps like Facebook, Snapchat, and Foursquare. One of our best mobile device forensic tools effectively recovers vast quantities of live and deleted device locations from the memory of Android smartphones and the file systems of iPhones.
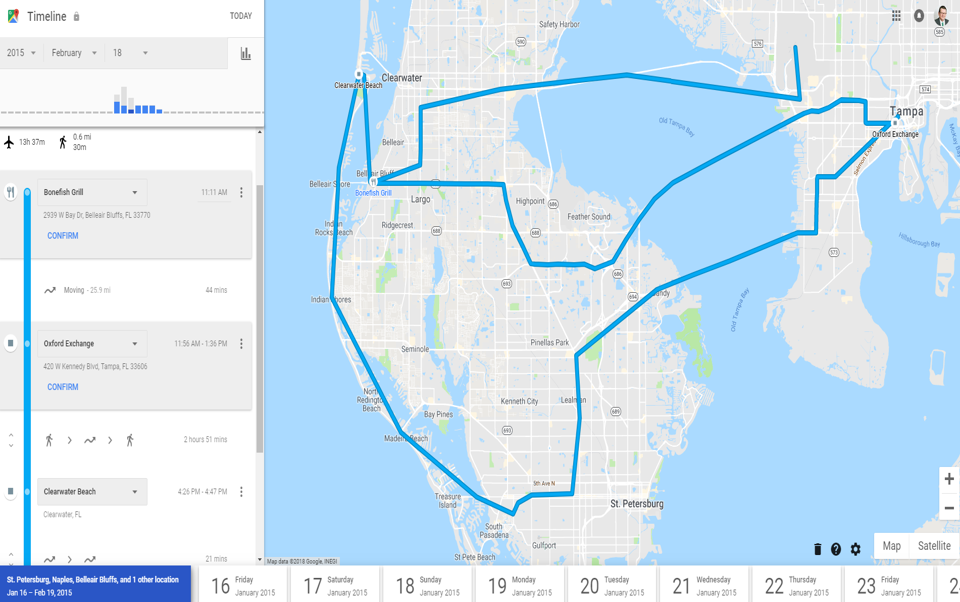
Carney Forensics develops maps and other visual exhibits of geolocations using Google Earth and Google’s Timeline as pictured below.
Cell Phones are Our Specialty
Our cell phone experts use forensic cell phone tools to recover evidence from over 39,000 makes and models of mobile devices. We also decode text messages, chats, and other evidence from over 877 unique mobile apps from our client’s iPhone or Android smartphones. We recover deleted and hidden evidence on every phone we examine. As a result, we have become experts at spoliation and fraud cases involving willful, intentional destruction of evidence.
We have learned to avoid reliance on just one forensic cell phone tool to recover essential mobile evidence. Cell phone forensic tools are diversified and operate independently from one another. Even the best tools have material strengths and weaknesses. As a result, dramatic differences in recovery performance and outcomes are common and expected in mobile forensic examinations. One tool may excel at recovering deleted text messages, another may have an angle on email, yet another may recover the most photographs and their metadata.
No single cell phone forensic tool can recover all the evidence from every device or every mobile app on that device. Based on our experience reviewing opposing counsel experts’ work product, we have noticed many cell phone investigators using just one tool. But, one tool is never enough! You don’t want to fail to recover the smoking gun evidence which may settle or win your client’s case because your expert didn’t take the time to use the best tools in the lab.
When cell phone experts accept the fact that “One tool is never enough” for all the valid reasons stated above, they obtain and train on a variety of cell phone forensic tools and put them into practice in their labs. This qualifies them to begin using the best practice of cross validation in which the expert performs artifact and metadata recovery comparisons across multiple mobile device forensic tools to better understand their mobile evidence.
Cross validation has value in determining “best evidence” for production. Which tool has recovered a greater quantity of material artifacts, or deleted artifacts? Which tool has recovered the most relevant metadata, possibly date and timestamps on the timeline, or GPS device locations for the relevant geography? Carney Forensics uses cross validation for best evidence production.
So, our cell phone experts use the four best cell phone forensic tools on the planet. They have different strengths to examine each cell phone that enters our lab to recover and decode absolutely all the digital evidence on which your case may turn. If one tool can’t find it, another will.
We Specialize in Advanced iPhone Forensics
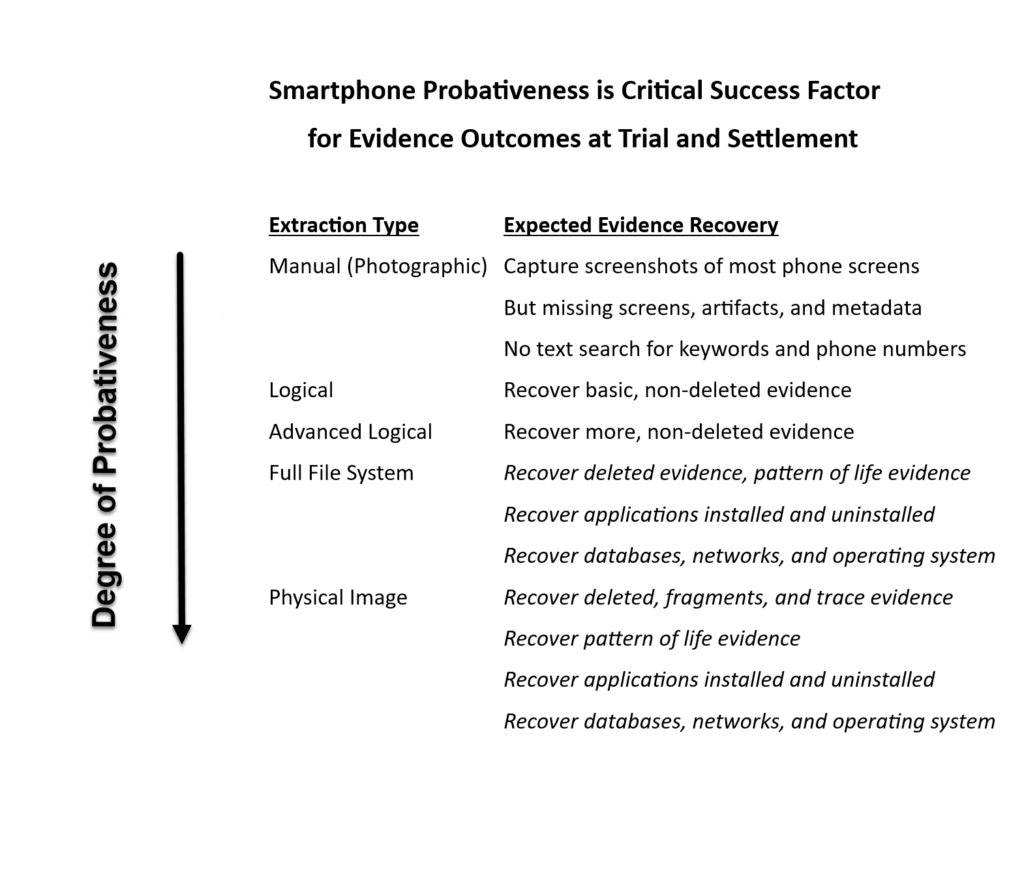
America’s most popular iPhone smartphone has become a materially important source of best evidence for civil and criminal litigation. However, the effectiveness of iPhone forensics to recover probative evidence was declining for a decade until a significant, transformational advance introduced in 2020 marked the return of iPhone forensics. This new cell phone imaging capability enables the recovery of vastly greater quantities of live and deleted iPhone evidence. It includes new forms of deeply probative evidence we have come to understand and apply successfully in court cases.
The cell phone expert must diligently find and produce the most probative extraction available to position the iPhone for optimal evidence recovery. The phone investigator must extract a deeply probative iOS full file system from the iPhone. No inferior iTunes backup extraction, not even an encrypted iTunes backup, will be enough. The phone expert must also extract an iOS keychain from the iPhone to decrypt mobile app data recovered in an encrypted state.
Carney Forensics has invested heavily in several cellphone forensics tools to extract iOS evidence from the broadest range of iPhone and iPad models. Imagine how you might use breakthrough iPhone forensics to discover messages, email, documents, media, fitness and health data, Google searches, Screen Time, and pattern of life evidence for advocacy in your next case.
We Offer Advanced Android Forensics
What about forensics for Android devices? 2024 has also brought meaningful innovations to Google’s mobile platform, which has been available since 2005. We can bypass most passwords and pattern locks. We can defeat encryption with advanced cell phone imaging to get deeply probative extractions instead of relying on disappointing Android backups. And, like iPhones, cell phone experts can now recover abundant, deleted evidence and new databases using Android forensics, which exposes pattern of life and digital wellbeing evidence for judicial review.
Carney Forensics has invested heavily in cellphone forensics tools to extract Android evidence from the broadest range of Samsung, LG, Motorola, OnePlus, and Google Pixel models. We also support cost-reduced Androids, today’s burner phone.
How might you use cutting-edge Android forensics to recover messages, emails, documents, media, fitness and health data, Google searches, and other evidence to settle your next case and avoid trial?
We Can Handle Your Cell Phone, Glitches and All
Whatever cell phone your client or opposing counsel may present, the cellphone experts at Carney Forensics can handle it. We perform phone imaging on legacy smartphones like BlackBerry, Windows Phone, and older Windows Mobile phones. We also support previous-generation feature phones like the Motorola RAZR and Nokia models. We also image and recover evidence from old flip phones and classic burners with their prepaid plans.
If your cell phone is damaged, even waterlogged, we can forensically repair it before cell phone imaging. We can unlock, recover, or bypass most passcodes that lock smartphones using bootloaders or advanced hardware techniques like JTAG, chip-off, and ISP.
We Have a “Plan B” if Your Cell Phone is Lost or Destroyed
If your cell phone has been lost, catastrophically destroyed, or traded in at the phone store for a new model, we have a long list of alternative evidence sources to discuss with you as we develop a “Plan B” for proving your case. Carney Forensics collects evidence from web-based, online, or “cloud” accounts to replace smartphone evidence. For instance, an Apple iCloud account can produce much of the same evidence as an iPhone. Similarly, a Google or Samsung account can substitute a good amount of evidence normally recovered from an Android device. Backups of smartphone data from the cloud, when forensically recovered, have the power to save your litigation.

You can obtain a subpoena return or ISP data from a subscriber consent authorization for evidence from Apple’s or Google’s subpoena compliance organization in their legal departments. Carney Forensics has forensic tools to parse and decode the evidence they provide for your review.
Vehicle Systems Forensics provides a “Plan B” in the form of evidence recovery from an automobile or truck infotainment system to which the smartphone was synchronized one or more times using a USB cable or Bluetooth connection.
Cell phone service provider business records, such as those from Verizon, T-Mobile, or AT&T, can be obtained by subpoena or subscriber consent authorization. These accurate records can include call logs, text message logs, and 4G LTE and 5G data records. They are sourced from the cell towers and base stations from which the cell phone communicates and exchanges data.
Last, if text message recovery is the goal of the forensic examination, the correspondent’s smartphone may be obtained by court order. This can provide an independent mobile device forensic examination to replace the custodian’s lost or destroyed smartphone in a quest to find the same messages on the other device.
Cell Phone Forensics FAQs
Digital evidence on a cell phone can help an attorney develop an evidence strategy that may determine his or her theory of the case and identify persuasive arguments. An expert witness can produce and testify to the cell phone evidence in court. Litigating it successfully can prove the client’s claims and defenses and win or advantageously settle the case.
In most legal cases, the cell phone investigator can recover and analyze the cell phone’s evidence and generate forensic tool reports for the legal team’s review for an average cost of $3,500 to $5,000. Each smartphone takes approximately 8 to 12 hours of lab time. Factors that go to cost include how much storage or memory capacity is built into the smartphone. How accessible the smartphone’s evidence is given possible damage, missing or incorrect passcodes, or data encryption. And how many hours of analysis are needed. Last, a critical factor is how many cell phone forensic tools are required to recover and analyze the material evidence upon which the dispute will turn, especially deleted or hidden evidence.
Most of the evidence will be found in the smartphone’s handset memory. Information related to the carrier and its cell tower network will be found in the SIM (Subscriber Identity Module) card. Media evidence like photographs and videos will be found on the microSD card for Android devices. However, often, the phone evidence is synchronized or backed up to online cloud accounts like Apple iCloud and Google and can be recovered there.
Before beginning cell phone imaging, it is essential to isolate the cell phone from signals or incoming data, such as cell towers, GPS satellites, Wi-Fi, Bluetooth, and NFC (Near Field Communication commonly used for mobile credit payments). To do this, the cell phone expert must power off the device, remove its SIM card, and place it in a Faraday bag. These steps ensure the original data is preserved and any data loss is avoided. Once the device is sufficiently isolated, the cellphone expert can properly acquire the digital evidence. Often, airplane mode, or flight mode, is used when the device is removed from the Faraday bag and powered on for examination.
Yes, often. Advanced capabilities are available for unlocking most iPhones except for the latest models. The news is even better for Android smartphones. Cellphone forensics tools for Android models use bootloaders, which can often bypass passcodes and extract the phone’s memory. The tools enable cell phone investigators to recover or remove passcodes from many Android models. They use advanced electronic acquisition techniques like JTAG, chip-off, and ISP extractions of phone memory to bypass passcode protection.
Generally, yes. The type and amount of deleted evidence recovered from a cell phone depend on several factors, including the phone’s make and model, how it was used, and the length of time since the evidence was deleted.
App evidence recovery from cell phones depends on the make and model of the cell phone and the particular app, which is the target of the goal of the examination. Every third-party app records the user’s data in different ways. It is difficult for the cell phone expert to know whether deleted information can or cannot be recovered from an app without analyzing the device and the app in question. The more popular the app, the better the chances to recover the evidence because of better support by more cell phone forensic tools.
It usually takes just overnight to recover the evidence. If picked up locally, Carney Forensics’ courier can usually return it the next day. If it is delivered to the lab by an overnight carrier, it usually takes a day or two. Please make sure all passcodes are available to the cell phone expert and report any cell phone damage.
Talk to the attorney or phone user to identify the device and then develop a plan of action for recovering its evidence. The attorney usually needs a deeply probative phone extraction to reveal deleted and hidden evidence. In contrast, the phone user needs a quick cell phone imaging outcome so the device is returned ASAP.
Packaging the phone:
Put the phone into flight or airplane mode.
Power the cell phone off.
To prevent the device from talking to the network or cell towers, wrap it with 3 to 5 layers of aluminum foil.
Bubble wrap or foam wrap the phone to protect it during shipping.
What else to include in the box:
If you have the data cable and power charger, send them along with the phone.
Document any passcode or pattern lock for the phone.
Document any damage or missing parts, such as a SIM card or a microSD card.
How to ship the phone:
Ship overnight with a signature required upon delivery to start the Chain of Custody.
Ship with a tracking number so the lab can locate the package in case of delay.


